Overview
This advisory address two related threat claims affecting institutions connected to Nigeria's financial sector. Around 27 March 2026, threat actor ByteToBreach posted a claim alleging compromise of a Top-tier bank data. Also, on the 31st of March 2026, the same actor posted a separate claim involving a renowned payment platform. At the time of drafting, there has been no public incident statement from the bank or the payment platform. This advisory therefore treats both events as unverified but credible enough to justify immediate defensive review.
The payment platform remains a high-impact payment and integration platform used by public- and private-sector organizations for collections, payroll, multi-bank payments, and related approval of workflows. Official documentation describes role-based access, transaction approval controls, REST-based integrations over HTTPS, and long-lived transaction reporting. The Federal Government also clarified in March 2025 that the payment platform would be integrated into the Treasury Management and Revenue Assurance System, alongside other approved providers, rather than continue as the sole TSA gateway. Even with that change, any compromise of the payment platform credentials, approval flows, or connected bank integrations could still have material downstream consequences.
Incident Timeline

Analytic Assumptions and Plausible Intrusion Paths
No public forensic findings were available at the time of reporting. The scenarios below are analytic assumptions derived from the actor's claims, public reporting on ByteToBreach's prior tradecraft, and official information about how the payment platform integrations and authorization workflows operate. They are intended to guide containment and threat of hunting, not to describe a settled incident record. A credential-led scenario, including use of infostealer-sourced credentials or previously exposed secrets, also remains plausible and could mean the reported scope is overstated.
Assumption A - Direct Exposure or API Abuse at the Bank
One plausible starting point is a web-facing application or API weakness at the bank. There is a possible indication that a Swagger/OpenAPI specification file was left accessible on a live production server, exposing a full map of active API endpoints. One such endpoint, reportedly a user-lookup path is alleged to have allowed direct retrieval of customer and employee records without adequate authorization controls. Public threat-intelligence reporting on ByteToBreach also links the actor to SQL injection and credential abuse in prior cases. If this breach claim reflects a real intrusion, the most plausible entry paths are one or more of the following:
- Unauthenticated or weakly authenticated API endpoints exposed to the internet, allowing direct data queries without reliable session or authorization controls.
- SQL injection or parameter manipulation against web-facing APIs or backend database queries.
- Credential reuse against administrative portals, partner interfaces, or support systems using credentials harvested from infostealer logs or prior leaks.
- Exposure of internal-only API routes, debug functionality, or test endpoints that become reachable from the public internet.
If access began this way, the likely next step would have been structured by extraction of customer, employee, and document records rather than opportunistic browsing.
Assumption B - Trusted-Relationship or Token Abuse Against the payment platform
A second plausible scenario is abuse of a trusted bank-to-platform relationship combined with a misconfigured cloud storage environment. Secondary reporting suggests the actor may have used access gained at the bank as a pivot point to reach the payment platform’s infrastructure, where a misconfigured S3 bucket is alleged to have been the primary exfiltration vector. Official platform documentation describes multi-bank access, API-based integrations, role-based workflows, and transaction authorization controls. If the bank or another connected institution stored active API secrets, access tokens, approval data, or integration configuration in a reachable system, an attacker could reuse those artifacts against the payment platform without exploiting a new software flaw in the platform itself.
The likely sequence is:
- The attacker identifies API credentials, service-account secrets, approval artifacts, or session tokens stored in a compromised bank environment.
- The attacker enumerates accessible records, beneficiary data, approval of workflows, or historical reports, then exfiltrates the highest-value datasets.
- Those artifacts are replayed or exchanged against the payment platform-facing interfaces, appearing as legitimate partner activity.
This scenario matters because supply-chain style abuse can occur even when the shared platform itself is not the initial point of compromise. In other words, trusted credentials may be enough.
Assumption C - Data Exfiltration, Leakage, and Possible Scope Inflation
ByteToBreach has been publicly profiled as a financially motivated actor that monetizes access and stolen data through underground forums, Telegram channels, and a public-facing victim-shaming site. In prior reporting, the actor has paired technical intrusion with structured data packaging and promotional proof samples. At the same time, KELA has warned that some actor 'breach' claims in the wider ecosystem may rely on credentials stolen by infostealer malware rather than a full enterprise compromise. For this case, both a genuine intrusion and a partially inflated claim should remain in scope until stronger evidence emerges.
Threat Actor Context - ByteToBreach
Public reporting places ByteToBreach in active underground operations since mid-2025. Threat-intelligence profiles describe the actor as financially motivated, focused on selling stolen data and access, and recurrently interested in financial services, telecoms, technology providers, and government-linked data. The actor's tradecraft appears opportunistic rather than ideologically driven.

The advisory relevance here is practical: even if the actor exaggerates scope, the combination of credential abuse, public leak promotion, and focus on financial data makes rapid containment and transaction review essential.
Data Reportedly Exposed
Alleged Claims of the Bank
The following categories were reportedly included in the actor’s post regarding the bank:
- Approximately 900,000 customer records including banking and transaction data.
- Approximately 3,000 employee records, including executive and board-level personal information.
- BVN and NUBAN account numbers.
- Identity documents such as passport copies and driver's licenses.
- Loan portfolio data and credit scores.
- Transaction histories.
Alleged Claims of the Payment Platform
Secondary reporting indicates the actor claimed to have exfiltrated approximately 3TB of data from a misconfigured cloud storage bucket associated with the payment platform. The alleged dataset includes a substantial volume of KYC documents alongside other sensitive materials. If the claim reflects genuine access, the most relevant confirmed and inferred data categories include:
- KYC documents and identity verification files (reportedly constituting approximately 800GB of the total exfiltrated volume)
- Live relational database exports (MySQL and PostgreSQL), application source code, container images, and HSM key material
- Password hash collections and credential stores, alongside beneficiary files, payroll-related data, and payment-routing details
- Payment transaction records, reconciliation data, mandate details, and customer or payer records processed through the platform’s collection and payment services
Recommended Actions
The actions below are prioritized against the three assumptions above: internet-facing API abuse, credential or token theft, and trusted relationship replay into a shared payments platform.
Priority 1 - Integration Integrity and Secret Rotation (0-24 hours)
- Revoke and reissue all the payment platform-related API keys, client secrets, OAuth tokens, service-account passwords, and stored approval artifacts.
- Review beneficiary details, routing data, standing instructions, payroll batches, webhooks, and approval workflow settings for unauthorized changes since 25 March 2026.
- Temporarily restrict the payment platform-facing API access to approved IP ranges where operationally possible and preserve pre-change configuration evidence.
- Request written incident status and credential-rotation guidance from the payment platform or your account representative and preserve that correspondence for audit and legal review.
Priority 2 - Identity and Access Controls (0-48 hours)
- Force password resets for privileged users, administrators, service accounts, and integration owners.
- Require multi-factor authentication on remote access, admin consoles, approval workflows, and any support tooling tied to payment operations.
- Review recent OAuth grants, API clients, and third-party app authorizations; disable anything not actively required.
- Search for exposed secrets in CI/CD pipelines, developer workstations, ticketing systems, wikis, scripts, and support attachments.
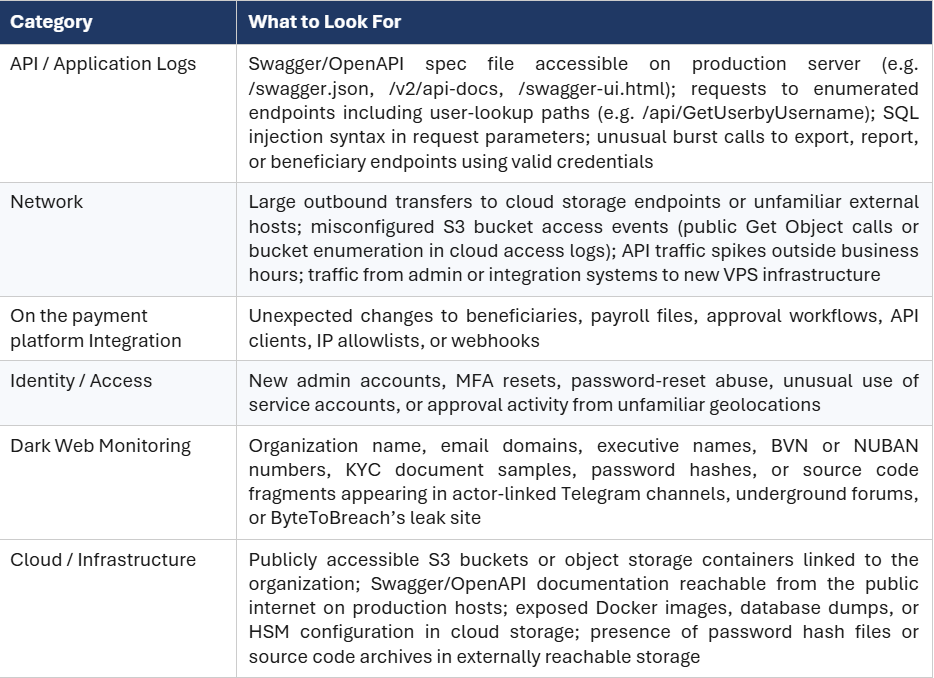
Priority 3 - Log Review and Threat Hunting (24-72 hours)
- Review web application, API gateway, WAF, and database logs from 20 March onward for SQL injection patterns, abnormal query volumes, off-hours enumeration, or repetitive access to export and reporting functions.
- Check for large outbound transfers, unusual REST API bursts, creation of new API clients, or use of valid credentials from unfamiliar IPs or geographies.
- Review administrative actions for new users, disabled controls, MFA changes, webhook changes, or newly approved beneficiaries.
- If your institution exchanges data with the bank, the payment platform, or both, review those integration logs separately and preserve them.
Priority 4 - Executive and Operational Awareness (48 hours)
- Brief executive leadership on elevated fraud, impersonation, and business-email-compromise risk if personal or transaction data has entered criminal channels.
- Apply enhanced out-of-band verification to unusual payment requests, beneficiary changes, payroll amendments, or emergency settlement instructions.
- Instruct staff to treat unexpected messages claiming to come from the bank, the payment platform, regulators, or payment counterparties with heightened caution.
Indicators of Compromise
No fully validated public IOC package for this campaign has been released. However, secondary reporting and leaked artefact analysis point to several technical indicators that can be used for immediate threat-hunting. Organizations should treat these as starting points and supplement them with environment-specific telemetry.








.png)
.png)