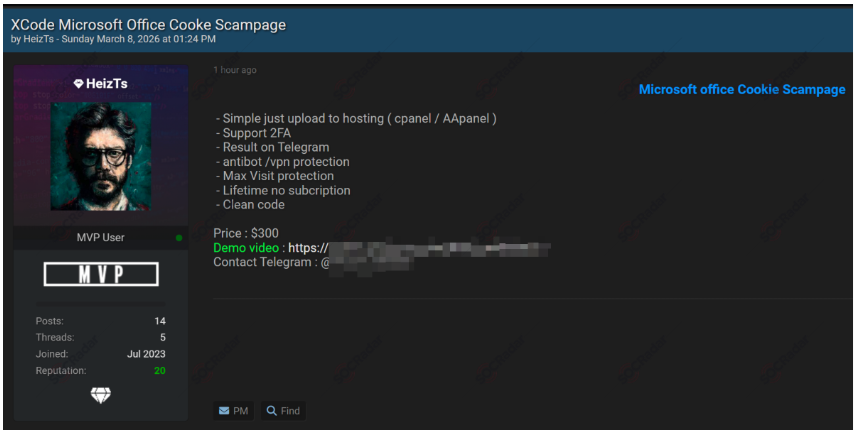
Threat intelligence monitoring has uncovered a new listing on a cybercriminal forum advertising a Microsoft Office "cookie scam page” phishing kit, a tool designed to steal login credentials and active session cookies from unsuspecting users. The kit is reportedly being sold for $300, highlighting how accessible sophisticated cybercrime tools have become in underground markets.
According to the forum post, the phishing kit imitates the Microsoft Office login interface, tricking victims into entering their credentials while quietly capturing both username/password combinations and authentication session cookies. These cookies can be especially valuable to attackers because they may allow them to hijack an authenticated session, potentially bypassing additional login requirements.
The seller promotes the tool as easy to deploy, claiming it can be uploaded to common web hosting panels such ascPanel or AApanel and used immediately without complex configuration.
Inside the Phishing Kit
Unlike older phishing pages that simply captured passwords, this kit appears to include advanced featuresdesigned to improve success rates and avoid detection. The seller advertises several capabilities, including:
- 2FA Support: The phishing page is designed to handle login attempts even when two-factor authentication is enabled.
- Session Cookie Harvesting: Captured session cookies may allow attackers to access accounts without repeatedly logging in.
- Antibot and VPN Protection: Built-in mechanisms block security researchers, scanners, or automated analysis tools from viewing the page.
- Max Visit Protection: Limits how many times the page can be accessed, reducing the chance of discovery.
- Real-Time Results via Telegram: Stolen credentials and cookies are instantly sent to the attacker through a Telegram bot.
- Lifetime Usage: The seller claims the tool requires no subscription and can be reused indefinitely.
The forum listing even includes a demovideo and a Telegram contact, suggesting that the seller is activelymarketing the phishing kit to potential buyers within the cybercriminalecosystem.
Why This Matters
Microsoft accounts are particularlyattractive targets because they often provide access to:
· Corporate email communications
· Cloud storage platforms
· Internal collaboration tools
· Sensitive business documents
Once compromised, these accounts can enable business email compromise (BEC), data theft, internal phishing attacks, or ransomware deployment within an organization.
The relatively low price of $300further lowers the barrier for entry, allowing even inexperienced threat actors to conduct professional-grade phishing campaigns.








.png)
.png)