APT 37
Operation Ruby Jumper · DPRK-Nexus Espionage
Hate to be the bearer of this news, but there’s a wild kid loose on the threat block and they’re bringing chaos with new campaigns
There’s a new campaign attributed to APT37, the DPRK-state-sponsored threat actor also tracked as ScarCruft, Ruby Sleet, and Velvet Chollima which entails deploying a suite of previously undocumented tools through weaponized Windows shortcut files, ultimately delivering persistent surveillance implants against targeted victims.
Who Is APT37?
APT37 is a long-standing cyber-espionage group operating on behalf of the Democratic People's Republic of Korea (DPRK).
How Ruby Jumper Operates
The campaign follows a multi-stage infection chain. A malicious LNK file serves as the entry point, triggering a sequence of newly identified loader tools before depositing the final surveillance implants. Each stage is designed to complicate detection and attribution.

The LNK-based initial access tactic is consistent with APT37's historically favored spear-phishing approach. What distinguishes Ruby Jumper is the deployment of four purpose-built intermediate tools, none of which appeared in prior APT37 campaigns indicating active tooling development within the group.
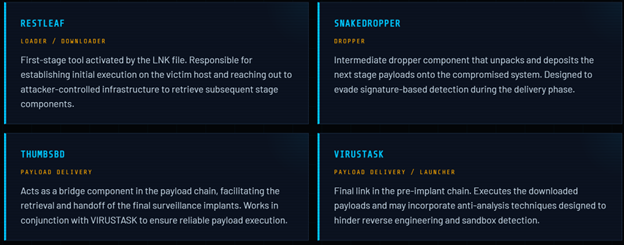
Four Undocumented Tools
There are previously undocumented tools used in the Ruby Jumper campaign to stage, load, and deliver the final payloads. Each plays a distinct role in the infection pipeline.
Surveillance Implants: FOOTWINE & BLUELIGHT
The culmination of the Ruby Jumper chain is the deployment of two implants with complementary surveillance capabilities. Together, they give APT37 persistent, broad-spectrum access to victim systems.
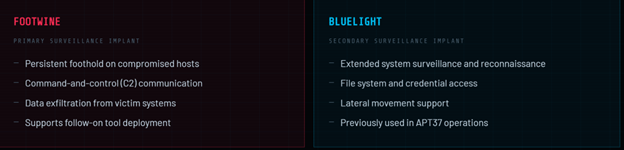
BLUELIGHT has been previously associated with APT37 activity, reinforcing attribution confidence. FOOTWINE appears to bea newer addition to the group's arsenal, purpose-built for this campaign's operational requirements.
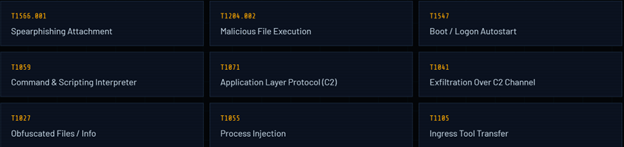
Relevant TTPs
Mitigation & Detection Guidance
- Block LNK execution from email and browser downloads: Enforce policies thar prevent shortcut files received via email or downloaded from the web from executing without explicit user approval. Consider disabling LNK file associations in high-risk environments.
- Deploy endpoint detection for multi-stage loaders: Tune EDR solutions to alert on process chains consistent with LNK → script interpreter → outbound download → secondary execution patterns, which are characteristic of RubyJumper's staging behavior.
- Hunt for RESTLEAF, SNAKEDROPPER, THUMBSBD, and VIRUSTASK indicators: Review endpoint telemetry for newly identified tool signatures and conduct retrospective threat hunting across historical logs.
- Monitor for BLUELIGHT and FOOTWINE implant behavior: Apply detection rules for known BLUELIGHT behaviors, including unusual C2 beaconing and file staging patterns. Extend these heuristics to cover FOOTWINE's related surveillance activities.
- Enforce strict email attachment controls: Apply sandboxing and detonation analysis to all inbound LNK, ZIP, and archive files. Blockmacro-enabled documents from untrusted senders.
- Patch and harden internet-facing infrastructure: APT37 has historically pivoted from initial access to exploit vulnerable services. Ensure internet-facing systems are patched and monitored for anomalous authentication and lateral movement activity.
IOCS
The following indicators were identified during analysis of the Ruby Jumper campaign.
Defenders should ingest these into SIEM, EDR, and network blocking tools immediately.
- Win32.Trojan.APT37
- Win32.Downloader.RESTLEAF
- Win32.Backdoor.ThumbsBD
- Win32.Backdoor.FOOTWINE
Host Indicators — File Hashes (MD5)
.png)
Network Indicators — Domains & IPs
.png)








.png)
.png)