On 13 March 2026, Microsoft released an urgent out-of-band security updateaddressing three Critical Remote Code Execution (RCE) vulnerabilities in the WindowsRouting and Remote Access Service (RRAS) management tool.
Theupdate, delivered as hotpatch KB5084597, targets Windows 11 versions 25H2and 24H2 and was deployed outside the standard monthly Patch Tuesday cycledue to the severity and immediate exploitability of the flaws identified.
Thevulnerabilities allow a remote threat actor to execute arbitrary code on anaffected device without requiring physical access.
About RRAS (Windows Routing and Remote Access Service)
TheWindows Routing and Remote Access Service (RRAS) is a native Windows Server anddesktop networking component that enables administrators to configure IProuting, VPN connectivity, and dial-up services. Because RRAS handles routingprotocol management and remote network access, it is a high-value target forthreat actors seeking to intercept traffic, manipulate network paths, or gainpersistent access to enterprise networks.
Affected Systems

Hotpatch Eligibility: KB5084597 isavailable only to devices explicitly configured for hotpatch delivery. Deviceson the standard Windows update channel will receive equivalent protectionthrough the scheduled update cycle and do not require manual intervention.
Vulnerability Detail
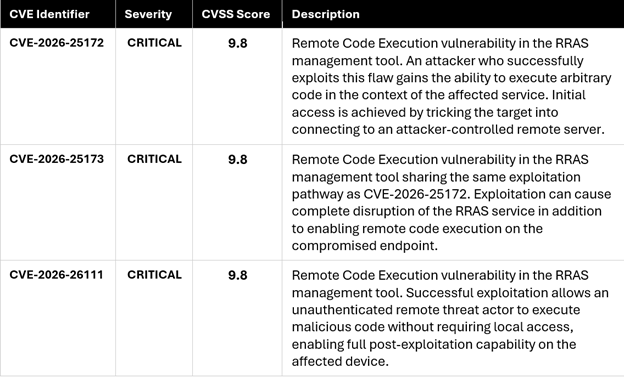
Microsoft identified three distinct flaws within the RRAS management tool, a core networking component used by administrators to configure routing protocols and VPN services. All three vulnerabilities share the same attack surface and exploitation pathway and are individually rated Critical.
Attack Vector and Exploitation Pathway
- The threat actor establishes a maliciouslycrafted remote server that mimics a legitimate RRAS management endpoint.
- The target user, typically a network administrator or privileged user, is tricked into connecting to this server through phishing, DNS manipulation, or adversary-in-the-middle (AiTM) techniques.
- Upon establishing the connection, theattacker’s server delivers a crafted payload that exploits the RRAS managementtool vulnerability.
- The exploitation results in: (a)disruption or crash of the RRAS management service, and/or (b) remotecode execution on the victim’s device in the context of the vulnerable process.
- Post-exploitation activity may includemalware deployment, credential harvesting, lateral movement to adjacent networksegments, or data exfiltration via the compromised VPN/routing infrastructure.
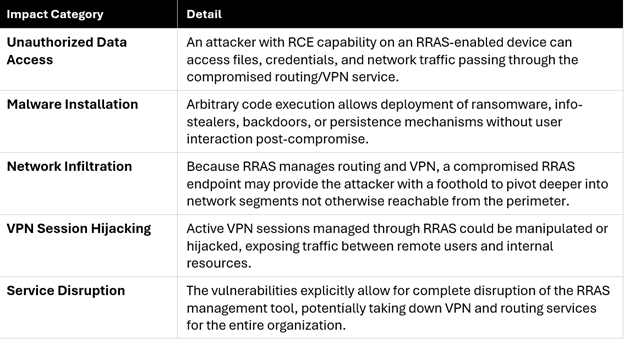
Potential Post-Exploitation Impact
Recommended Actions
- Verify Windows Update is activeand enabled on all hotpatch-eligible Windows 11 endpoints. The hotpatch willdownload and install automatically once Windows Update is enabled.
- Audit network security logs for any unusual outbound connections to unknown remote servers, particularly fromhosts running RRAS-enabled configurations. Unexplained outbound connectivity on VPN-related ports may indicate exploitation attempts.
- Assess whether any networkadministrators or privileged users with RRAS management access have recently beenconnected to unfamiliar remote servers. Initiate an incident investigation intoany confirmed or suspected pre-patch connections.
- Implement or review network segmentation controls around RRAS-enabled infrastructure. Ensure that RRAS management traffic is restricted to known, authorized management network segments and not exposed to general user-accessible zones
- Ensure endpoint detection andresponse (EDR) tooling is deployed and current on all RRAS-hosting devices todetect post-exploitation behavior if patching is delayed orincomplete.








.png)
.png)