A familiar social-engineering campaign has returned with a dangerous upgrade: attackers are now deploying a brand-new backdoor family after hijacking remote sessions through Microsoft Teams and Windows Quick Assist, and it is considerably harder to detect than anything this group has used before.
The threat actors behind the activity are now deploying a new malware family dubbed A0Backdoor, extending previously observed tactics linked to Blitz Brigantine/Storm-1811, a financially motivated group associated with Black Basta ransomware operations.
From Email Bombing to Full Compromise

The campaign typically begins with:
- Email bombing, overwhelming the target’s inbox with junk mail.
- The victim is then contacted via Microsoft Teams by an impersonated “internal IT support” representative offering assistance.
- The attacker instructs the employee to open Windows Quick Assist, a legitimate remote‑support tool that grants screen-sharing and remote control.
Microsoft has previously warned about this exact technique used by Storm‑1811, including Teams messages and calls from spoofed IT help desk accounts.
Signed MSI Installers
Source:
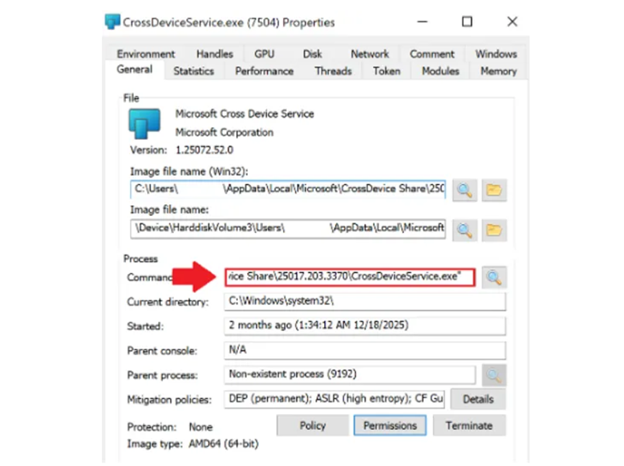
Once Quick Assist access is granted,attackers deploy digitally signed MSI installers disguised as legitimate Microsoft Teams components or Cross Device Service packages.
- Some malicious MSIs were hosted on Microsoft personal cloud storage via tokenized links, adding false legitimacy.
- Installers drop files into AppData directories mimicking authentic Microsoft software paths.
- They use DLL sideloading to launch malicious code undetected.
One example, Update.msi, replaced the legitimate .NET hostfxr.dll with a malicious copy to loadattacker code while appearing normal.
The Loader & Anti‑Analysis Behavior
The loader is built to evade detection,featuring:
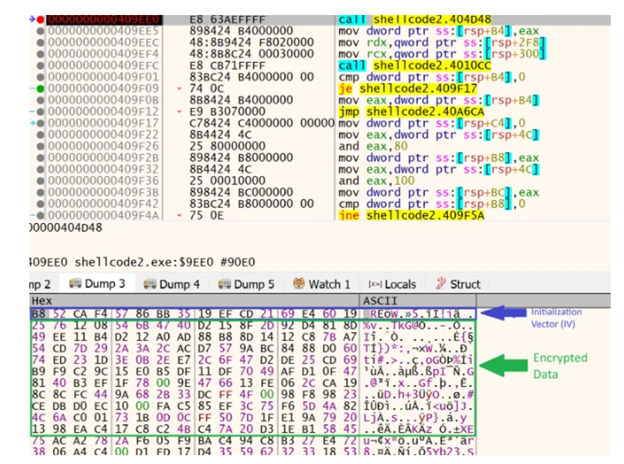
- Runtime decryption
- Massive thread creation
- Sandbox and virtualization checks (e.g., QEMU detection)
If analysis is detected, the loaderintentionally corrupts its own decryption process.
The A0Backdoor
The final payload, A0Backdoor, is a memory-residentbackdoor that:
- Fingerprints the infected host
- Exfiltrates and receives covert commands using DNS tunneling, specifically MX record lookups via public resolvers like 1.1.1.1
- Avoids traditional C2 infrastructure, making detection harder
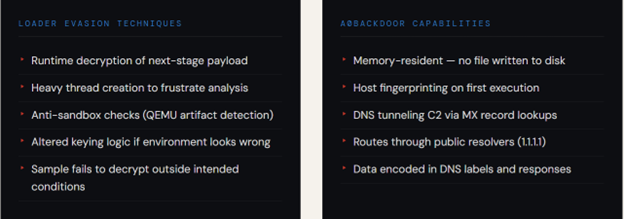
This design bypasses many DNS‑filteringtechniques focused on TXT-based tunneling or overt C2 domains.
This campaign highlights similar patternstied to Black Basta, Cactus ransomware, and Storm‑1811 activity.
Mitigations
- Disable or block Windows Quick Assist via Group Policy where remote support is not operationally required. Where needed, restrict to approved IT accounts only.
- Configure Microsoft Teams to clearly flag and log all messages from external organizations. Train staff to treat unsolicited external contact as a potential social-engineering attempt.
- Alert on any signed MSIinstaller or Microsoft-branded binary appearing in user-writable directories (%AppData%, %LocalAppData%, %Temp%).
- Tune DNS monitoring to detectanomalous MX record query volume and high-entropy DNS labels, not just TXT record abuse. Inspect queries routing through 1.1.1.1 and 8.8.8.8 forunusual patterns.
- Monitor for DLL loads fromuser-writable paths particularly any process loading hostfxr.dll or similar .NETcomponents from non-system directories.
- Implement rules to detect sudden high-volume inbound email surges against individual mailboxes. Use this as a trigger for enhanced monitoring of that user's subsequent Teams activity.








.png)
.png)