You know the popular “You can’t touch this “Line by MC Hammer, that’s how every staff and every organization should aim to be this new quarter, Untouchable!
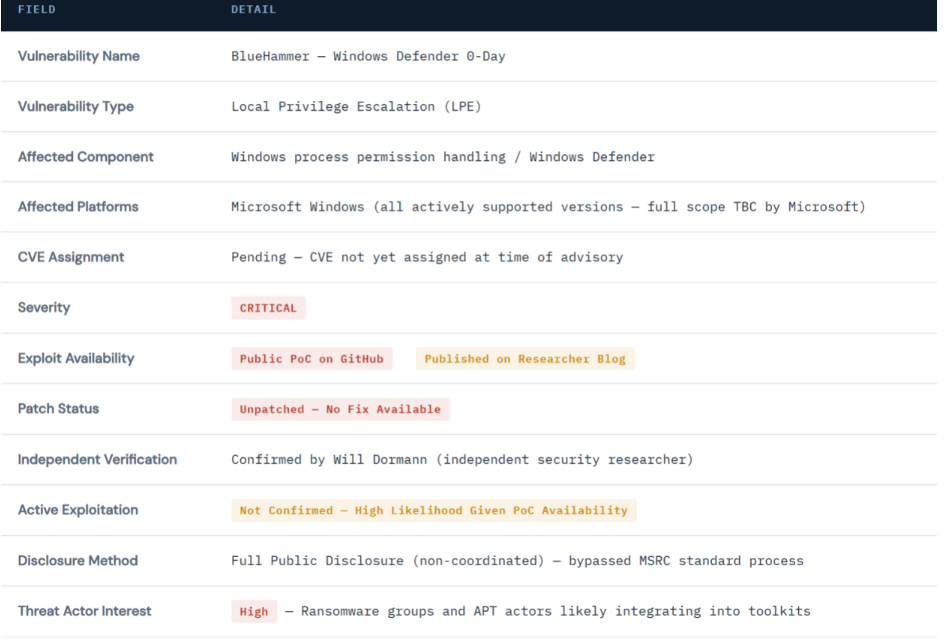
A critical zero-day vulnerability referred to as BlueHammer, has been publicly disclosed in Microsoft Windows, affecting how Windows processes handle permission checks. The flaw allows low-privileged users or malware already present on a system to escalate their access to full system-level control, a technique commonly referred to as privilege escalation.
At the time of writing, Microsoft has not released a patch, security update, or official mitigation guidance. All organizations running Windows environments, particularly those relying on Windows Defender as a primary security control are considered at elevated risk.

The vulnerability resides in how Windows processes handle certain permission checks. Under normal operation, Windows enforces strict access controls that prevent low-privileged user accounts from accessing sensitive system resources.
BlueHammer exploits a flaw in this enforcement mechanism, creating a pathway through which a standard user or malware operating in a low-privilege context, can acquire SYSTEM-level privileges.

Technical Analysis
This type of weakness is classified as a Local Privilege Escalation (LPE) vulnerability. It does not grant initial access to a machine on its own, but when combined with an initial foothold (e.g., via phishing, a malicious download, or exploitation of an unpatched application), it provides attackers with the ability to bypass all access restrictions and take complete control of the affected system.

Vulnerability Reference Data
Detection Guide
Security operations teams should tune their detection rules and hunting queries to surface behaviors consistent with BlueHammer exploitation. The following patterns are indicative of privilege escalation activity and should be treated as high-priority alerts in the current threat environment.

Recommended Mitigations & Defensive Actions
Monitor for Unusual Privilege Escalation Activity
- Configure SIEM alerts and EDR rules to detect anomalous privilege changes, particularly token impersonation, process injection, and unexpected SYSTEM-level process spawning.
- Review existing alert thresholds many default configurations do not flag low-and-slow privilege escalation patterns.
Enforce Least Privilege Access Across All Systems
- Audit all user accounts and service accounts for excessive permissions. Remove administrative rights from standard user accounts where not operationally required.
- Privilege escalation exploits are substantially less impactful when users operate at genuinely minimal privilege levels.
Deploy or Tune Advanced EDR Solutions
- Ensure your endpoint detection and response tooling is configured to identify suspicious behaviour consistent with LPE attempts including unusual process privilege chains, credential dumping, and LSASS access.
- Verify that EDR agents are fully deployed and telemetry is feeding into centralised monitoring.
Restrict Unnecessary User Permissions & Application Controls
- Implement application whitelisting or allow listing to prevent execution of unauthorized binaries including PoC executables.
- Review and restrict user rights assignments in Group Policy, particularly "Act as part of the operating system", "Debug programs", and "Create a token object".
Segment Networks and Limit Lateral Movement Paths
- Enforce network segmentation between high-value systems and general user workstations.
- Ensure that SYSTEM-level access on one machine does not provide direct pathways to domain controllers or sensitive data stores.
esentry CTI Response & Ongoing Monitoring
The esentry Cyber Threat Intelligence team is actively monitoring the BlueHammer situation across multiple intelligence sources, including dark web forums, threat actor channels, and open-source repositories. The following actions are underway on behalf of all active clients:
ACTIVE
Dark Web Monitoring for BlueHammer Exploit Kits
Scanning threat actor forums, marketplaces, and ransomware group communications for BlueHammer references, toolkits, or active campaign indicators.
ACTIVE
IoC Development & Distribution
Extracting, validating, and publishing indicators of compromise from the known PoC codebase and any observed in-the-wild activity. Updated IoCs will be pushed to client environments and our GitHub repository.
ACTIVE
Microsoft Patch Tracking
Monitoring Microsoft's MSRC communications, Patch Tuesday schedule, and out-of-band update channels for any BlueHammer remediation. Clients will be notified immediately upon patch availability.
PLANNED
Client Environment Vulnerability Assessment
Conducting targeted assessments of client environments to identify exposure to BlueHammer attack vectors, including privilege configurations, EDR coverage gaps, and monitoring blind spots.








.png)
.png)